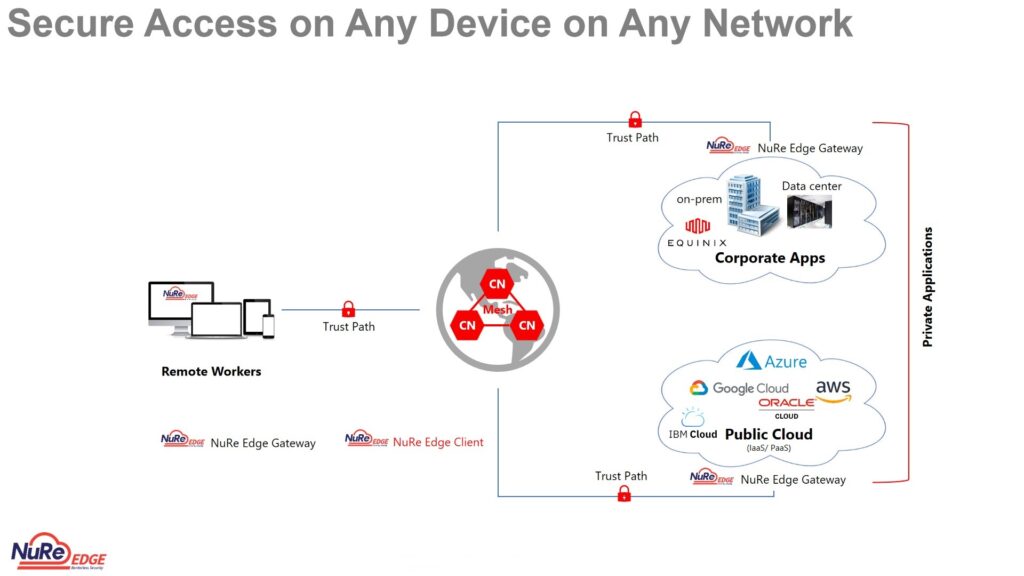
Get fast, seamless and secure access to private applications using cloud-delivered 3i’s AI-ML based CyberSecurity Mesh.
A Cybersecurity Mesh That Does It All!
3i Secure Private Access (SPA) is a cloud service that provides fast, seamless and Zero Trust Access to private applications running on the public cloud or within data centres without relying on legacy VPN. With SPA, applications are never exposed to the internet, making them inaccessible to unauthorised users and protecting data and resources with application-level access control based on user identity and device security posture.
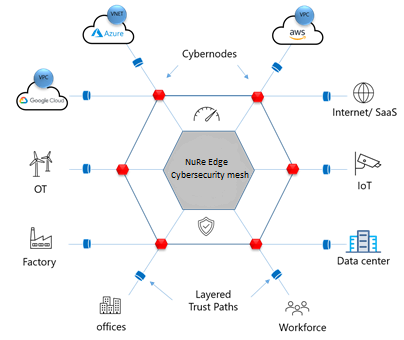
SPA allows organisations to phase out legacy VPN hardware and move towards a more secure, cloud-first, remote access architecture. End the high capital investment, refresh cycles and ongoing management costs of VPN appliances. SPA drastically reduces the complexity of network and security architectures, accelerating cloud adoption. With SPA, User Access is based on policies created by the workspace admin within the 3i Admin Console, resulting in a simple, secure, and effective way to access internal applications.
How It Works
Intelligent Platform Ecosystem for Secure Digital Transformation
Adjacent to the internal applications running in a public cloud, data centre, or an on-premise server, 3i Secure Private Access places a small piece of software called Cyber Gateway (CGW), deployed as a container or a VM, which is used to extend a highly secure Zero Trust Path out to 3i AI/ML based Cybersecurity Mesh.
The CGW establishes an outbound connection and does not receive any inbound connection requests, thereby preventing DDoS attacks.3i Secure Private Access utilises a lightweight Client installed on a Microsoft Windows, Apple macOS, iOS, Android or a Linux device. The 3i Client steers Private Access application traffic to the Cybersecurity Mesh using either DNS or the IP address.
A Closer Look
Our service ensures both the user devices and the CGW use battle-tested hardware root-of-trust, eliminating man-in-the-middle attacks. A Mesh Node approves access and stitches together the user-to-application session. SPA is 100% software-defined, so it requires no appliances and allows users to benefit from the cloud and mobility while maintaining the security of their applications.
SPA gives Workspace Admins control over applications and the users authorized to access them. Workspace Admins create and manage user groups, applications, and application groups within the 3i Admin Console.
Why Choose Us
The 3i Advantage
3i AI/ML-based Cybersecurity Mesh runs our SPA service and is built on 5G technology. This gives our cloud security services advantages over legacy providers that made their tech years ago. Specifically, we deliver:


 Dr. Madan Bhalchandra Gosavi (B.A. (Hons.), LLM, M.Phil, PhD)
Dr. Madan Bhalchandra Gosavi (B.A. (Hons.), LLM, M.Phil, PhD) Mr. Umesh Mehta
Mr. Umesh Mehta Mr. Raj Kumar Ahuja
Mr. Raj Kumar Ahuja
 Harish Shenoy
Harish Shenoy CA Uttam Prakash Agarwal
CA Uttam Prakash Agarwal Uttam Jhunjhunwala
Uttam Jhunjhunwala
 Ranjit Balakrishnan
Ranjit Balakrishnan Emmanuel N
Emmanuel N Ramu Bodathulla
Ramu Bodathulla
 Rangapriya Goutham
Rangapriya Goutham Kiran Chittar
Kiran Chittar Sushant Purushan
Sushant Purushan
 Nilesh Gupta
Nilesh Gupta Mohan TS
Mohan TS Sanjay Rawa
Sanjay Rawa Dr. Aruna Sharma
Dr. Aruna Sharma Mr.Avtar Singh Monga
Mr.Avtar Singh Monga Mr. Thompson P. Gnanam
Mr. Thompson P. Gnanam Ms. Zohra Chatterji
Ms. Zohra Chatterji Dr. Kalyan Krishnamoorthy
Dr. Kalyan Krishnamoorthy







 Mr. Pravir Vohra
Mr. Pravir Vohra Viraf Sirvala
Viraf Sirvala

 Amrita Gangotra
Amrita Gangotra