Endpoint Data Backup Services
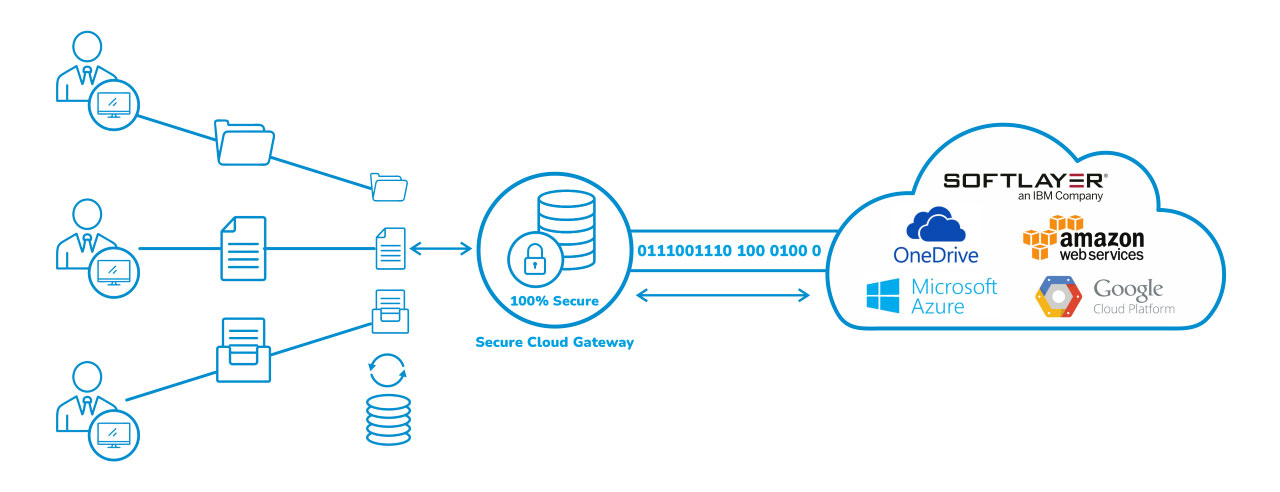
Endpoint Data Backup Services strengthen and make your cloud storage environments fail-safe. Our encryption-enabled, scale-able and cost-effective cloud data security solutions help enterprises and organizations take control of their data and ensure that files and data move safely between organization assets and the cloud.
Workflow of Backup as a service
Key features & benefits
- Centralized policy-based management and enterprise-class auditing, meeting your compliance objectives
- Easy, self-service restores, enhancing visibility and employee data access making it risk free
- Integrates seamlessly and securely with an enterprise’s Lightweight Directory Access Protocol(LDAP) or Active Directory namespaces
- Scale easily to multiple geographies as the business grows, enabling effective use of data across regions
- Optimize flow-control based on network bandwidth availability with network throttling to reduce server instability
- Optimize storage usage with compression and data duplication, resulting in longer retention periods
- Partial file transfer capability ensures that only changed data gets moved, which stems duplication
Enterprise Backup & DR as a Service
A. The best way to protect data against hardware failures, data breaches, or ransomware attacks is to have a secure backup. It is paramount for organizations to ensure the safety of end-user data to maintain business continuity.
NuRe 3i’s Enterprise Backup as a Service enables you to strengthen the backup process and make your cloud storage environments safe.
Key features
- Encryption-enabled, giving an additional layer of security to protect your critical business data
- Scalable on demand backup services, to meet your ever-changing business requirements
- Cost-effective, as it simplifies management, streamlines compliance and ensures maximum value from data
- Data security, helping you take absolute control of data, ensuring that files and information are always safe
- Role-Based Access Control (RBAC) enabled, restricting access, thereby reducing scope of data leaks
B.Disaster Recovery as a Service (DRaaS)
DRaaS from NuRe 3i is affordable and efficient image-based, which always ensures availability of applications. It is data and platform agnostic.
Key Features
- Fast, flexible fail-over of specific Virtual Machines or an entire site, with settings specific to different modes.
- streamlined fail-back with zero data loss and minimal disruption to users, while minimizing network traffic
- Recovery assurance, including support for replica and fail-over testing and alternating production between sites.
- Seamless integration with user interfaces, workflows and data collection, making the process hassle-free
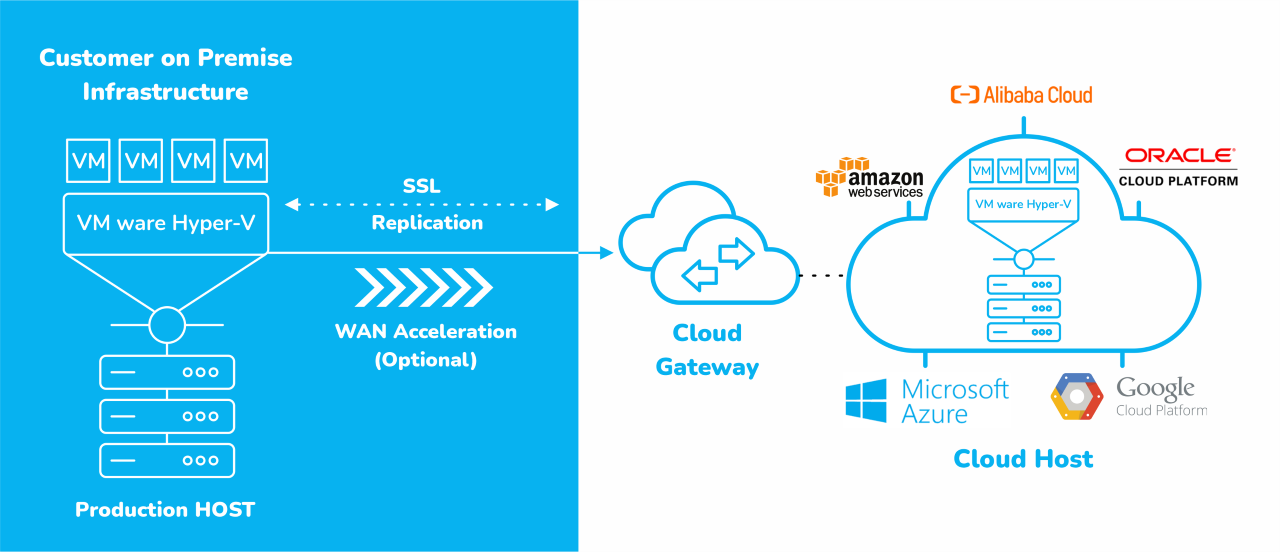
Workflow of DRaaS
Security as a Service
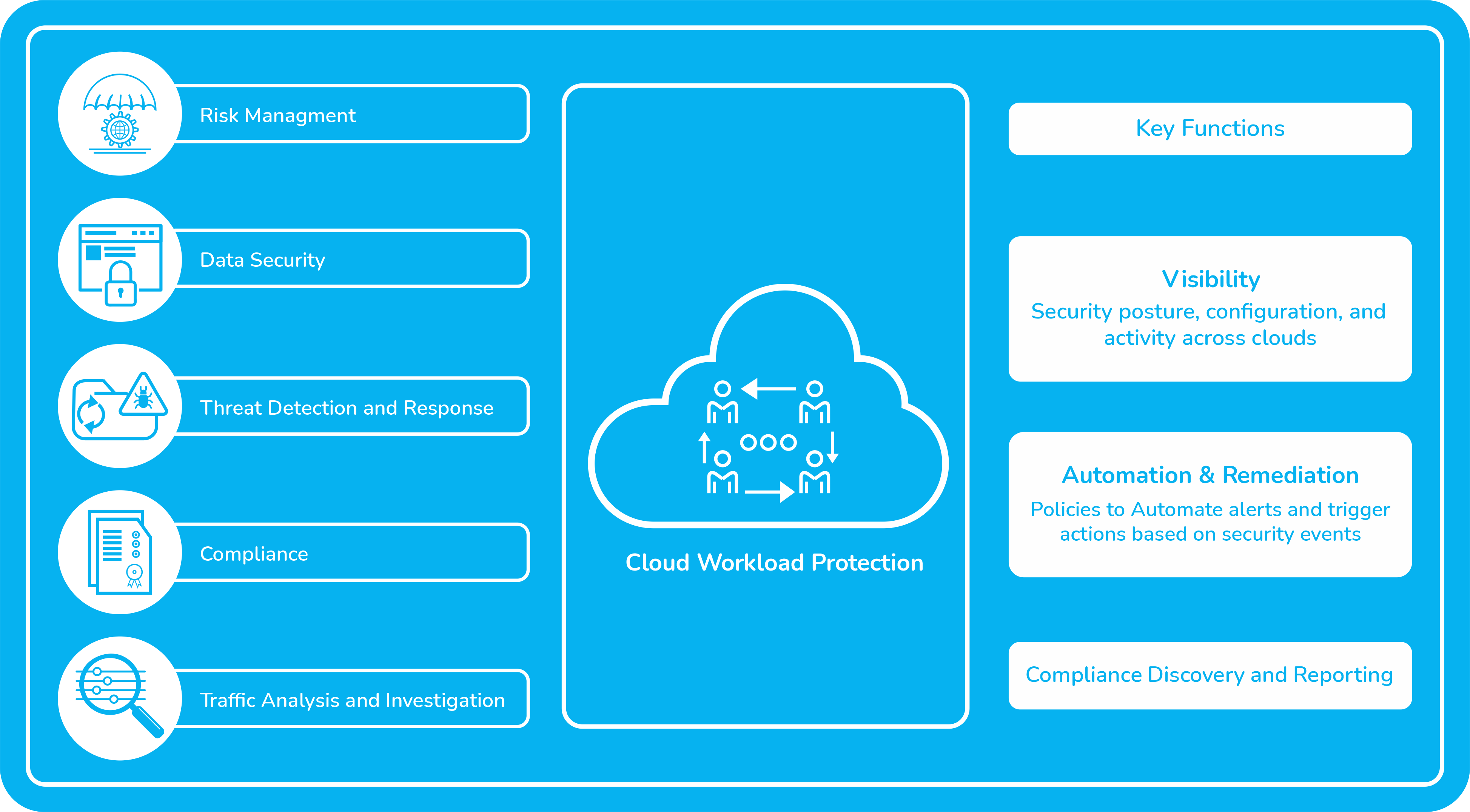
3i Infotech’s SECaaS offers security administrators the ability to evaluate their cloud configuration security posture, detect potential threats originating from misconfiguration of cloud resources, analyze traffic across cloud resources, and evaluate cloud configuration against best practices. It gives them the ability to manage risk across multi-cloud infrastructures, ensures regulatory compliance reporting, and incorporates remediation into the cloud infrastructure life cycle automation framework.
Workflow of SECaaS
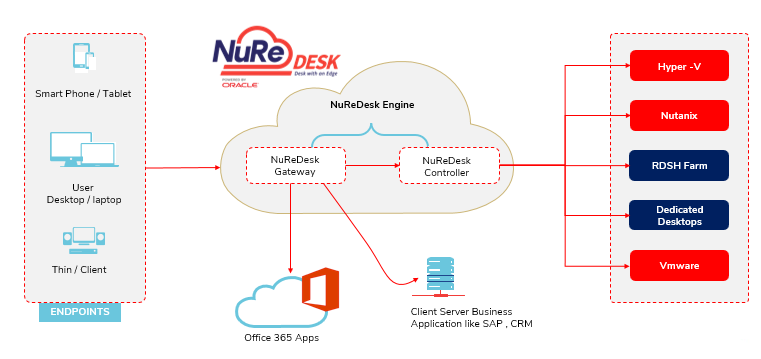
NuRe Desk
NuRe desk is a next-generation virtual desktop solution that has a virtualization engine to provide users with a highly secure and seamless experience. It also manages various desktop environments for data centers, remote offices, and mobile and cloud users.
NuRe desk VDI technology replaces the traditional VPN for secure remote access with zero trust network access. NuRe Desk provides a managed desktop solution that empowers business users to deploy and manage applications & desktops from a centralized console. The NuRe Desk OS acts as a shared host for virtualized Windows Desktops, Applications, Networks, and Storage on the organization’s endpoint devices – PCs, thin clients, or smartphones, simplifying the management of endpoints
Key benefits :
- Easy web based management of multiple devices
- Seamless secure Virtual desktops in minutes
- Pool Multiple Virtual desktop and manage them easily
- Deployed on geo-native OCI platform for maximum availability and reliability


 Dr. Madan Bhalchandra Gosavi (B.A. (Hons.), LLM, M.Phil, PhD)
Dr. Madan Bhalchandra Gosavi (B.A. (Hons.), LLM, M.Phil, PhD) Mr. Umesh Mehta
Mr. Umesh Mehta Mr. Raj Kumar Ahuja
Mr. Raj Kumar Ahuja
 Harish Shenoy
Harish Shenoy CA Uttam Prakash Agarwal
CA Uttam Prakash Agarwal Uttam Jhunjhunwala
Uttam Jhunjhunwala
 Ranjit Balakrishnan
Ranjit Balakrishnan Emmanuel N
Emmanuel N Ramu Bodathulla
Ramu Bodathulla
 Rangapriya Goutham
Rangapriya Goutham Kiran Chittar
Kiran Chittar Sushant Purushan
Sushant Purushan
 Nilesh Gupta
Nilesh Gupta Mohan TS
Mohan TS Sanjay Rawa
Sanjay Rawa Dr. Aruna Sharma
Dr. Aruna Sharma Mr.Avtar Singh Monga
Mr.Avtar Singh Monga Mr. Thompson P. Gnanam
Mr. Thompson P. Gnanam Ms. Zohra Chatterji
Ms. Zohra Chatterji Dr. Kalyan Krishnamoorthy
Dr. Kalyan Krishnamoorthy







 Mr. Pravir Vohra
Mr. Pravir Vohra Viraf Sirvala
Viraf Sirvala

 Amrita Gangotra
Amrita Gangotra